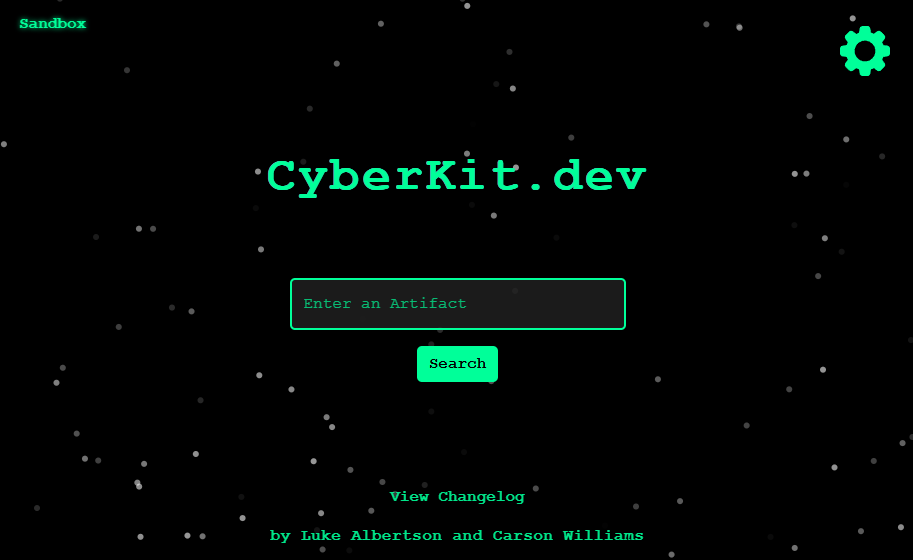
CyberKit.dev
The Problem
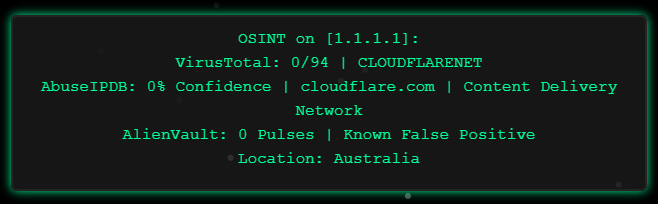
After starting as a security analyst, I consistently found myself manually typing out OSINT details for the IPs, hashes, and domains I came across in alerts. Usually something along the lines of this:
1
2
3
4
5
OSINT on [1.1.1.1]:
VirusTotal: 0/94 | CLOUDFLARENET
AbuseIPDB: 0% Confidence | cloudflare.com | Content Delivery Network
AlienVault: 0 Pulses | Known False Positive
Location: Australia
This was a tedious time sink - so Luke Albertson & I automated it.
The Solution
Having already setup my domain and website through Cloudflare pages I explored what other services and capabilities were available. This lead to my discovery of Cloudflare ‘Workers’. As per the AI summary I just got from Google, “Cloudflare Workers are a serverless execution environment that allows developers to deploy code globally at the edge of Cloudflare’s network”. Building my tool with Workers allowed me to make it globally accessible while also providing me with some cloud experience.
How it works:
User Input (Frontend) – A React app on Cloudflare Pages lets users enter an IP, domain, or hash.
Classification – The frontend detects the artifact type (IP, domain/URL, or hash) using regex.
Processing (Backend) – Based on the artifact type, the request is routed to one of three dedicated Cloudflare Worker APIs (IP, domain/URL, or hash), each of which queries multiple OSINT sources (e.g., VirusTotal, AbuseIPDB, AlienVault, URLScan) and returns aggregated results.
Seconds later, the results are returned and are report-ready.
Check it out here: CyberKit.dev or here: osint.lukealbertson.com or even here: osint.carsonww.com